Cyber Security Awareness Month 2023
This year marks the 20th anniversary Cybersecurity Awareness Month campaign! Since 2004, the President of the United States and Congress have declared October to be Cybersecurity Awareness Month, helping individuals protect themselves online as threats to technology and confidential data become more commonplace.
The VCU Information Security Office is celebrating Cyber Security Awareness Month by highlighting these important security topics:
The use of strong passwords and trying a password manager.
Becoming aware of multifactor authentication fatigue, and adding 2 factor authentication for person accounts too!
Recognizing and report phishing. You can report phishing to our email mailto:infosec@vcu.edu
Why it is important to update software.
Lastly, be sure to check out the "Helpful Security Tips/Hints!" for tips and tricks related to cyber security.
October 25: Update Your Software
- The importance of Software Updating?
- How to do it?
- Best practices?
- Backup your shit.
This week we want to discuss updating your computer software. You may not realize it, but cyber attacks are constantly looking for weaknesses (aka vulnerabilities) in software you run on your phone and computer. If a bad person exploits these weaknesses (aka vulnerabilities) they may be able to install malware or trojans on your computer. Malware can remotely control your computer, steal your passwords, and gain access to files on your computer! Software vendors are constantly updating their software to fix these weaknesses (aka vulnerabilities) but it is your responsibility to install these updates.
How updating works:
When a software vendor discovers a bug or weakness (aka vulnerabilities) in their software, they will create a software update to fix the problem. Often applications may update several times a week. These updates may also include new features and improvements. Software updates happen on mobile devices such as an iPhone or Android phone and even your laptop. Software updates can either happen automatically or manually. Automatic updates will update whenever the software detects there is an update. It doesn't require your assistance but you may need to restart your computer/device. Manual updates must be downloaded and installed by you. While this gives you control over when to update, it can be difficult to manage or easy to forget.
Here are some tips for software updates:
- Update Often - Don’t delay when there is a software update!
- Get it from the source - Once download software updates from reputable sources. Never use pirated, hacked or otherwise illegally versions of software. These type of software often come with malware!
- Make it automatic - You should set the security updates to happen automatically. Most vendors provide this solution. You can turn on automatic updates for Windows 10/11, macOS, iOS, and even Android.
Watch out for fakes! - If you are surfing the web and you see a sudden pop-up to update your software, these are typically fake. Most software will automatically load from the application (e.g Zoom, Chrome, Word, etc) and you do not need to download a separate file.
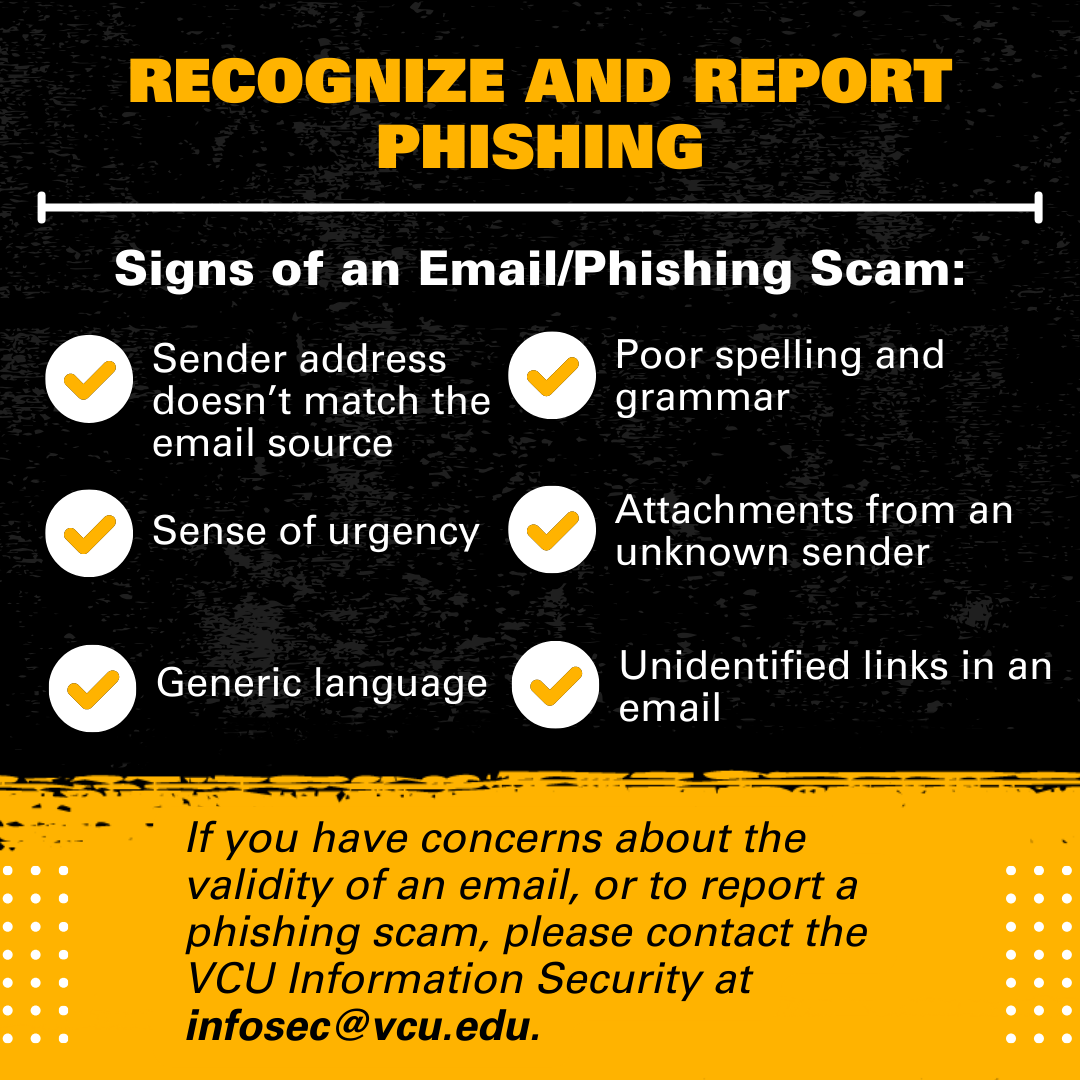
October 19: Email Proper Use (Sending and Receiving)
We are going to break up this week’s cybersecurity focus on Receiving Emails and Sending Emails. Depending on whether receiving or sending emails, we’ll want to take different items into account.
Receiving Email:
When you receive an email, your primary concern will be phishing. Phishing is a cybercrime in which a target or targets are contacted by email, telephone, or text message by someone posing as a legitimate institution. Over the years, phishing has become more sophisticated. Phishers can even spoof email addresses!
At VCU, your Information Security hosts a Phishing Blog where we post phishing samples and inform the community about phishing attacks that are happening at VCU.
Here are some recent phishing scams you should be aware of:
- Fake Job/Intern Scam: This scam works by offering you a lot of money for a little bit of work. The scammer sends you a check for more than what they initially agreed to pay, you cash the check and send some money back to the scammer. The check is a fraudulent check and will bounce in a couple of days, leaving you on the hook for the full amount.
- Paypal Invoice Scam: The scammer pretends to be a vendor and sends you an invoice. As long as you do not pay the invoice, you will stay safe!
- Extortion Scam: The scammer pretends they have hacked your computer and threatens to exhort you for money. Don’t be fooled by this tactic.
If you receive a phishing or suspicious email, forward it to our Information Security Office at infosec@vcu.edu for us to review. If you report it, we’ll enter you in our monthly Security Hero Raffle where you have a chance to win a cool shirt.
Sending Email:
Although you may not think of sending emails as a security concern, there are a couple of aspects we’d like to highlight. While email can be used to send certain sensitive information, it may not always be the best option when transmitting highly sensitive information. It is important for us to consider what we are sending and who are the recipients. When sending the following information we recommend enforced encrypting in Gmail and password-protecting any documents with the following information:
- Payment card information
- Social Security Numbers/Driver's License Numbers with names and/or other identifiers - Confidential Personally-Identifying Information (PII)
- HIPAA Protected Health Information
- Other regulated information
Additionally, a good practice when you are emailing a group of students or a group of patients is to include those recipients in the BCC field to maintain privacy. The BCC field protects the privacy of email addresses in the original message. Recipients will receive the message, but won't be able to see the addresses listed in the BCC field
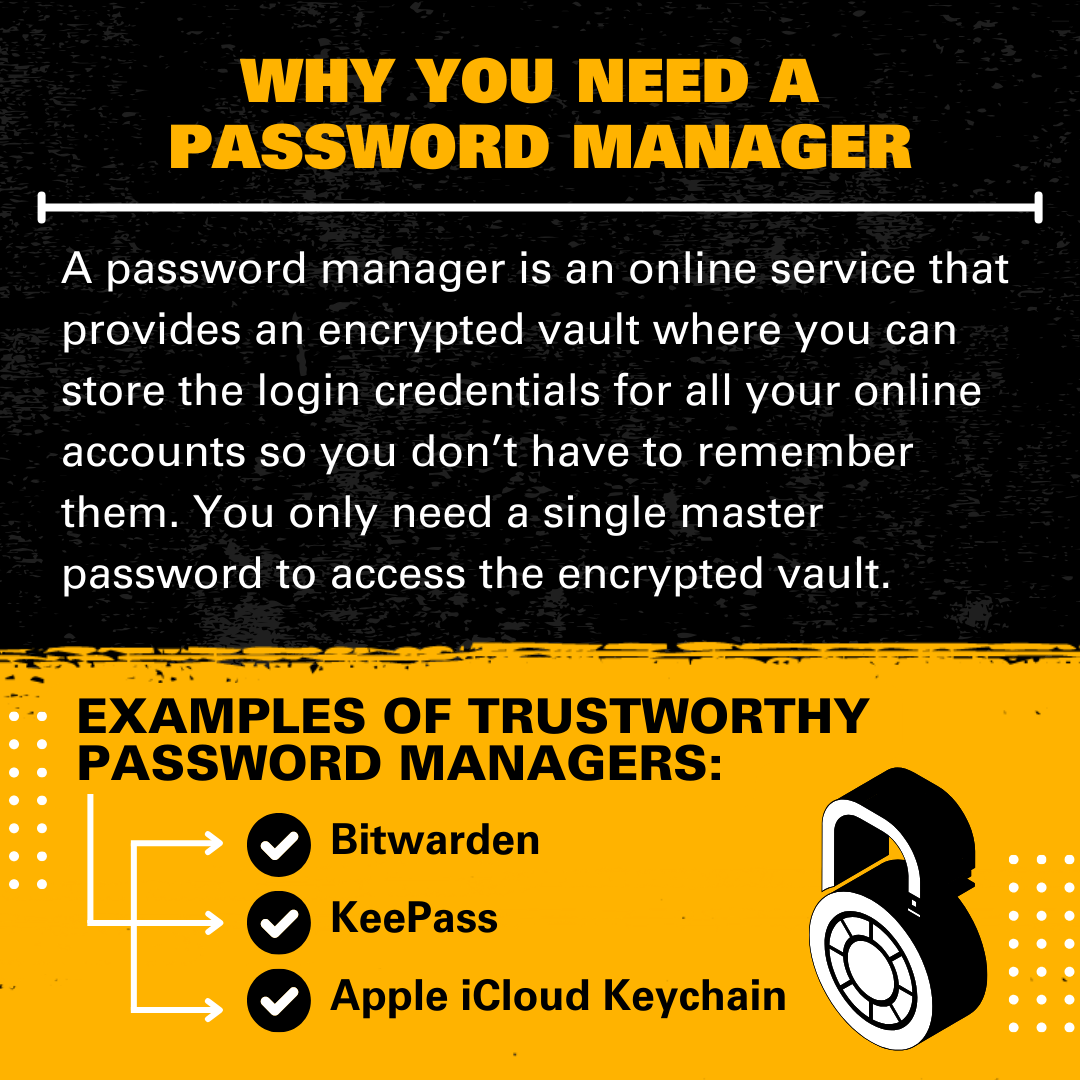
October 10: Password Management and Password Hygiene
What is password management?
Password management is a set of principles and best practices to be followed by users while storing and managing passwords in an efficient manner to secure passwords as much as they can to prevent unauthorized access.
What is a password manager?
A password manager (or a web browser) can store all your passwords securely, so you don't have to worry about remembering them. This allows you to use unique, strong passwords for all your important accounts (rather than using the same password for all of them, which you should never do).
The downside to password reuse and caution?
Reusing passwords makes it possible for a malicious agent to hack into an account to have access to others belonging to the same user. And the more a password is reused, the greater the risk of having the credentials breached
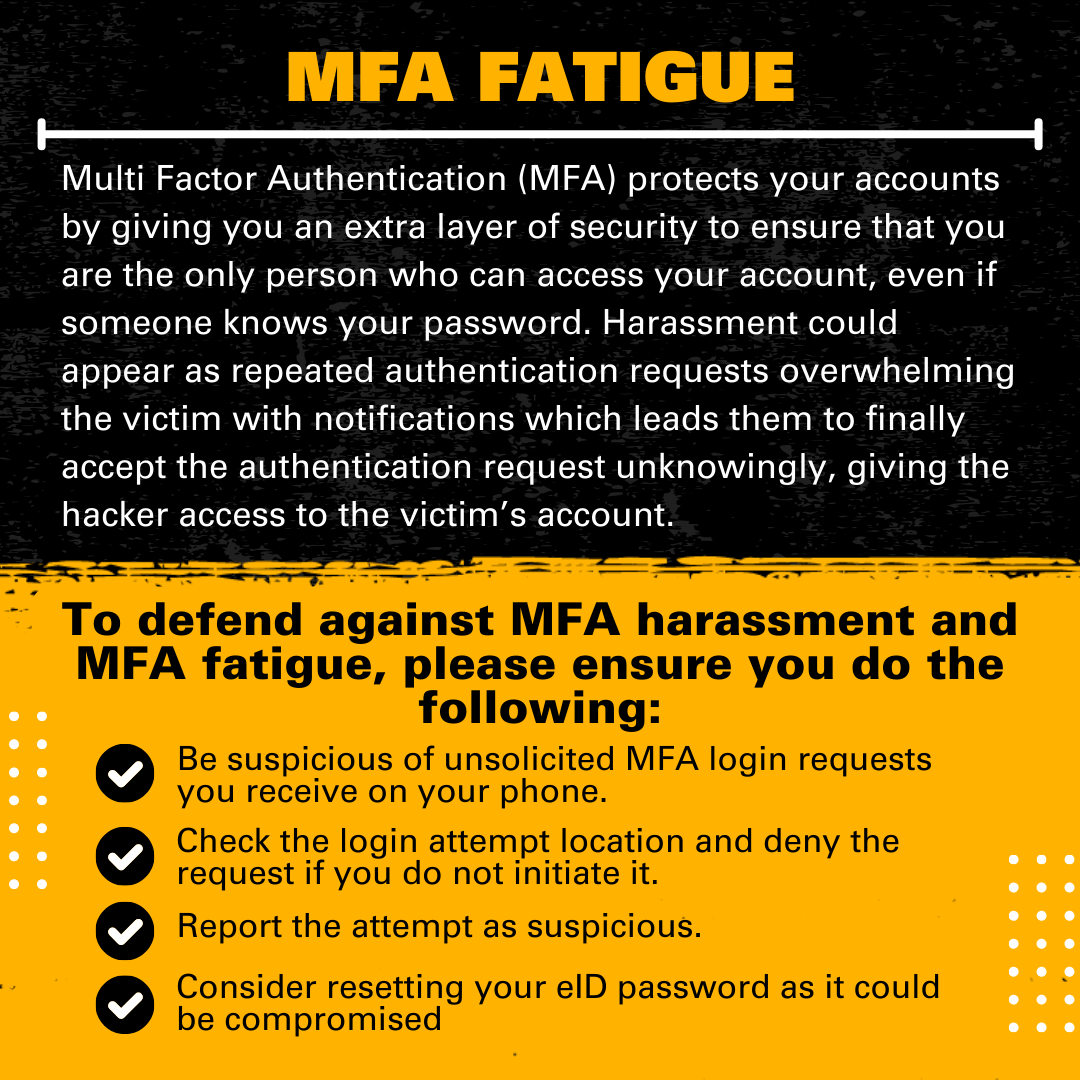
October 3: Multi-Factor Authentication Fatigue
We all know about Multi-Factor Authentication, right?
Multi-factor Authentication (MFA) is an authentication method that requires the user to provide two or more verification factors to gain access to a resource such as an application, online account, or a VPN. It is an extra layer of security to ensure that you are the only person who can access your account, even if someone knows your password. VCU account access requires your eID, Password, and a Device.
Well, what if you unexpectedly receive a push notification from Duo?
Is that a Duo notification? I didn't log in to anything?
Suddenly notice your phone blowing up with Duo notifications?!
Multi-factor authentication (MFA) fatigue (aka MFA Prompt Spamming/MFA bombing) is a technique used by attackers to flood a user's authentication app with push notifications in the hope they will accept, enabling the attacker to gain entry to an account or device. This technique only works if the threat actor already has the credentials of a targeted account from a previous compromise such as phishing, credential replay, brute forcing, password spraying, or from password reuse.
If you suspect that you are a victim of MFA fatigue please contact ITSC at 828-2227 to change your password, and report the incident to infosec@vcu.edu. If you don’t recognize the Duo push, do not respond.
How do I manage my MFA devices?
You can manage your devices within eid.vcu.edu. You can delete and add new devices. The video will show you How to Manage 2FA Devices at VCU.
If you need help setting up a new phone with DUO, please contact ITSC at 828-2227 or itsc@vcu.edu
* As of August 12th, DUO enrollment is required for all current and former students, staff, and faculty. *
*** On June 30th, 2022, VCU is disabling the SMS text messaging option in Duo as a method of authentication ***
“It's Easy to Stay Safe Online — See Yourself in Cyber.” #CyberForUs and #BeCyberSmart.
What is Cyber-Hygiene?
Cyber hygiene refers to fundamental cybersecurity best practices that an organization's security practitioners and users can undertake. As you have personal hygiene practices to maintain your own health, cyber hygiene best practices help protect the health of your organization's network and assets.
Below you will find helpful guides to improve your Cyber-Hygiene:
Tips for Protecting Yourself
- Always use passphrases on your computer.
- Longer passwords with letters and numbers (and special characters if supported) can help to keep your data safe.
- Lock your computer when you step away.
- On Windows, press [Windows + L].
- On Mac, press [Control + Shift + Eject] or [Control + Shift + Power].
- Never share your passwords with anyone.
- No VCU official or employee will ever ask you for your password.
- Use updated anti-virus and anti-spyware tools, plus a firewall.
- VCU provides anti-virus software for use on- and off-campus.
- All widely-available consumer operating systems (Windows, Mac OS X, and Linux) provide built-in firewalls. Just make sure your firewall is on
- Back your data up.
- Use a trusted, reputable online storage company, or officially-provided VCU network storage space.
- Consider encrypting your data.
- Handle information with care.
- Be careful when handling, transmitting, or storing sensitive or regulated information.
- Think before you click.
- Be aware of phishing emails and scam websites.
- If some sounds too good to be true, it probably is!
- Learn the signs of phishing emails
- Be aware of theft.
- Lock your doors and keep your personal belongings with you
.png)
.png)
.png)